This May 31st is Quit Facebook Day, but I won’t be deleting my account. No, I got rid of it a few weeks ago. As much as I’d like to claim that this was entirely some kind of ethical stance, the simple truth was that I didn’t actually make much use of the service. If I had the same negative feelings about Twitter, quitting would be a much tougher decision.
Should you leave Facebook? Maybe. It’s certainly a question that a lot of people are asking. Then, if they decide to, they ask ‘so how the hell do I delete the thing?’ Enough that this has become a Google suggested result:

There’s actually a website dedicated to helping you find the elusive ‘delete’ hidden in the unnecessarily complicated settings. You can find out how well you have protected your privacy at Profile Watch. There’s also a handy bookmarklet at Reclaim Privacy that will similarly assess your profile. For a laugh, you can also read through some posts of other Facebook users, who probably think they are talking to their friends, not the entire internet: Openbook.

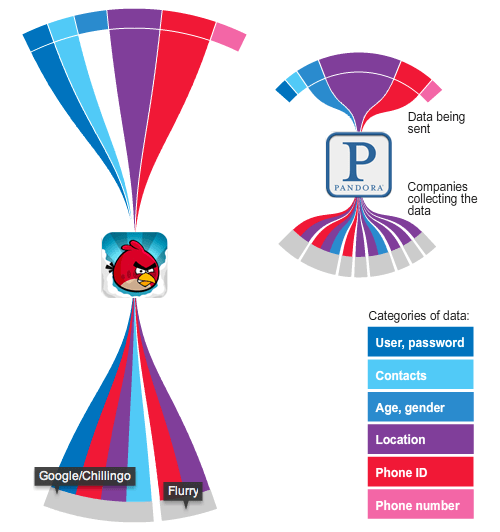
Are there real reasons to be worried? Well, after Facebook held a developer conference, lots of worried Google engineers left. And Google has hardly earned any privacy gold stars. And then there’s Mark Zuckerburg, the man behind the company, with a few thoughts on privacy (taken from an IM conversation when he was creating the service, then called The Facebook):
Zuck: Yeah so if you ever need info about anyone at Harvard
Zuck: Just ask.
Zuck: I have over 4,000 emails, pictures, addresses, SNS
[Redacted Friend’s Name]: What? How’d you manage that one?
Zuck: People just submitted it.
Zuck: I don’t know why.
Zuck: They “trust me”
Zuck: Dumb fucks.
Business Insider also has a fascinating expose on Zuckerburg. Decide for yourself if it holds much water, and if you think his character is likely to have improved in the last six years.
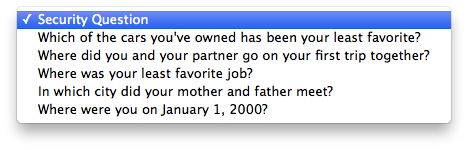
It’s also interesting to witness how Facebook has eroded the default privacy settings over the years, from friends and family to almost completely exposing everything.

While most users may not understand/care about these issues, there are plenty who do. Enough that when a new project to create an open-source distributed social network asked for $10,000 to get started, they were overwhelmed with donations. As I write this, they have over $170,000 pledged.
So I guess Facebook just gives me the creeps.
Continue reading →
![]() Datahole is a Twitter account I have been ‘maintaining’ for over four years. In practice I’ve simply been letting it run itself.
Datahole is a Twitter account I have been ‘maintaining’ for over four years. In practice I’ve simply been letting it run itself.